This is post 9 out of 10 in the LXC 1.0 blog post series.
Some starting notes
This post uses unprivileged containers, this isn’t an hard requirement but makes a lot of sense for GUI applications. Besides, since you followed the whole series, you have those setup anyway, right?
I’ll be using Google Chrome with the Google Talk and Adobe Flash plugins as “hostile” piece of software that I do not wish to allow to run directly on my machine.
Here are a few reasons why:
- Those are binaries I don’t have source for.
(That alone is usually enough for me to put an application in a container) - Comes from an external (non-Ubuntu) repository which may then push anything they wish to my system.
(Could be restricted with careful apt pining) - Installs a daily cronjob which will re-add said repository and GPG keys should I for some reason choose to remove them.
(Apparently done to have the repository re-added after dist-upgrades) - Uses a setuid wrapper to setup their sandbox. Understandable as they switch namespaces and user namespaces aren’t widespread yet.
(This can be worked around by turning off the sandbox. The code for the sandbox is also available from the chromium project, though there’s no proof that the binary build doesn’t have anything added to it) - I actually need to use those piece of software because of my work environment and because the web hasn’t entirely moved away from flash yet…
While what I’ll be describing below is a huge step up for security in my opinion, it’s still not ideal and a few compromises have to be made to make those software even work. Those are basically access to:
- pulseaudio: possibly recording you
- X11: possibly doing key logging or taking pictures of your screen
- dri/snd devices: can’t think of anything that’s not already covered by the first two, but I’m sure someone with a better imagination than mine will come up with something
But there’s only so much you can do while still having the cool features, so the best you can do is make sure never to run the container while doing sensitive work.
Running Google chrome in a container
So now to the actual fun. The plan is rather simple, I want a simple container, running a stable, well supported, version of Ubuntu, in there I’ll install Google Chrome and any plugin I need, then integrate it with my desktop.
First of all, let’s get ourselves an Ubuntu 12.04 i386 container as that’s pretty well supported by most ISVs:
lxc-create -t download -n precise-gui -- -d ubuntu -r precise -a i386
Let’s tweak the configuration a bit by adding the following to ~/.local/share/lxc/precise-gui/config (replacing USERNAME appropriately):
lxc.mount.entry = /dev/dri dev/dri none bind,optional,create=dir lxc.mount.entry = /dev/snd dev/snd none bind,optional,create=dir lxc.mount.entry = /tmp/.X11-unix tmp/.X11-unix none bind,optional,create=dir lxc.mount.entry = /dev/video0 dev/video0 none bind,optional,create=file lxc.hook.pre-start = /home/USERNAME/.local/share/lxc/precise-gui/setup-pulse.sh
Still in that same config file, you’ll have to replace your existing (or similar):
lxc.id_map = u 0 100000 65536 lxc.id_map = g 0 100000 65536
By something like (this assume your user’s uid/gid is 1000/1000):
lxc.id_map = u 0 100000 1000 lxc.id_map = g 0 100000 1000 lxc.id_map = u 1000 1000 1 lxc.id_map = g 1000 1000 1 lxc.id_map = u 1001 101001 64535 lxc.id_map = g 1001 101001 64535
So those mappings basically mean that your container has 65536 uids and gids mapped to it, starting at 0 up to 65535 in the container. Those are mapped to host ids 100000 to 165535 with one exception, uid and gid 1000 isn’t translated. That trick is needed so that your user in the container can access the X socket, pulseaudio socket and DRI/snd devices just as your own user can (this saves us a whole lot of configuration on the host).
Now that we’re done with the config file, let’s create that setup-pulse.sh script:
#!/bin/sh PULSE_PATH=$LXC_ROOTFS_PATH/home/ubuntu/.pulse_socket if [ ! -e "$PULSE_PATH" ] || [ -z "$(lsof -n $PULSE_PATH 2>&1)" ]; then pactl load-module module-native-protocol-unix auth-anonymous=1 socket=$PULSE_PATH fi
Make sure the file is executable or LXC will ignore it!
That script is fairly simple, it’ll simply tell pulseaudio on the host to bind /home/ubuntu/.pulse_socket in the container, checking that it’s not already setup.
Finally, run the following to fix the permissions of your container’s home directory:
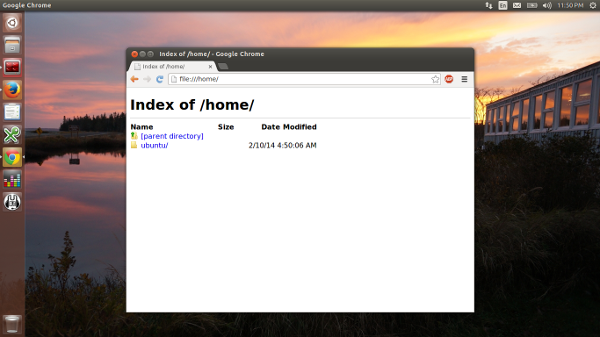
sudo chown -R 1000:1000 ~/.local/share/lxc/precise-gui/rootfs/home/ubuntu
And that’s all that’s needed in the LXC side. So let’s start the container and install Google Chrome and the Google Talk plugin in there:
lxc-start -n precise-gui -d lxc-attach -n precise-gui -- umount /tmp/.X11-unix lxc-attach -n precise-gui -- apt-get update lxc-attach -n precise-gui -- apt-get dist-upgrade -y lxc-attach -n precise-gui -- apt-get install wget ubuntu-artwork dmz-cursor-theme ca-certificates pulseaudio -y lxc-attach -n precise-gui -- wget https://dl.google.com/linux/direct/google-chrome-stable_current_i386.deb -O /tmp/chrome.deb lxc-attach -n precise-gui -- wget https://dl.google.com/linux/direct/google-talkplugin_current_i386.deb -O /tmp/talk.deb lxc-attach -n precise-gui -- dpkg -i /tmp/chrome.deb /tmp/talk.deb lxc-attach -n precise-gui -- apt-get -f install -y lxc-attach -n precise-gui -- sudo -u ubuntu mkdir -p /home/ubuntu/.pulse/ echo "disable-shm=yes" | lxc-attach -n precise-gui -- sudo -u ubuntu tee /home/ubuntu/.pulse/client.conf lxc-stop -n precise-gui
At this point, everything you need is installed in the container.
To make your life easier, create the following launcher script, let’s call it “start-chrome” and put it in the container’s configuration directory (next to config and setup-pulse.sh):
#!/bin/sh CONTAINER=precise-gui CMD_LINE="google-chrome --disable-setuid-sandbox $*" STARTED=false if ! lxc-wait -n $CONTAINER -s RUNNING -t 0; then lxc-start -n $CONTAINER -d lxc-wait -n $CONTAINER -s RUNNING STARTED=true fi PULSE_SOCKET=/home/ubuntu/.pulse_socket lxc-attach --clear-env -n $CONTAINER -- sudo -u ubuntu -i env DISPLAY=$DISPLAY PULSE_SERVER=$PULSE_SOCKET $CMD_LINE if [ "$STARTED" = "true" ]; then lxc-stop -n $CONTAINER -t 10 fi
Make sure the script is executable or the next step won’t work. This script will check if the container is running, if not, start it (and remember it did), then spawn google-chrome with the right environment set (and disabling its built-in sandbox as for some obscure reasons, it dislikes user namespaces), once google-chrome exits, the container is stopped.
To make things shinier, you may now also create ~/.local/share/applications/google-chrome.desktop containing:
[Desktop Entry] Version=1.0 Name=Google Chrome Comment=Access the Internet Exec=/home/USERNAME/.local/share/lxc/precise-gui/start-chrome %U Icon=/home/USERNAME/.local/share/lxc/precise-gui/rootfs/opt/google/chrome/product_logo_256.png Type=Application Categories=Network;WebBrowser;
Don’t forget to replace USERNAME to your own username so that both paths are valid.
And that’s it! You should now find a Google Chrome icon somewhere in your desktop environment (menu, dash, whatever…). Clicking on it will start Chrome which can be used pretty much as usual, when closed, the container will shutdown.
You may want to setup extra symlinks or bind-mount to make it easier to access things like the Downloads folder but that really depends on what you’re using the container for.
Obviously, the same process can be used for many different piece of software.
Skype
Quite a few people have contacted me asking about running Skype in that same container. I won’t give you a whole step by step guide as the one for Chrome cover 99% of what you need to do for Skype.
However there are two tricks you need to be aware of to get Skype to work properly:
- Set “QT_X11_NO_MITSHM” to “1”
(otherwise you get a blank window as it tries to use shared memory) - Set “GNOME_DESKTOP_SESSION_ID” to “this-is-deprecated”
(otherwise you get an ugly Qt theme)
Those two should be added after the “env” in the launcher script you’ll write for Skype.
Apparently on some NVidia system, you may also need to set an additional environment variable (possibly useful not only for Skype):
LD_PRELOAD=/usr/lib/i386-linux-gnu/mesa/libGL.so.1
Steam
And finally, yet another commonly asked one, Steam.
That one actually doesn’t require anything extra in its environment, just grab the .deb, install it in the container, run an “apt-get -f install” to install any remaining dependency, create a launcher script and .desktop and you’re done.
I’ve been happily playing a few games (thanks to Valve giving those to all Ubuntu and Debian developers) without any problem so far.
 Github
Github Twitter
Twitter LinkedIn
LinkedIn Mastodon
Mastodon
lxc-start -n precise-gui -d; lxc-ls --fancylxc_container: command get_cgroup failed to receive response
NAME STATE IPV4 IPV6 AUTOSTART
——————————————-
precise-gui STOPPED – – NO
———————————————————
please, give me full config ~/.local/share/lxc/precise-gui/config
my system
uname -aLinux vasilisc 3.13.0-8-generic #27-Ubuntu SMP Fri Feb 7 02:01:37 UTC 2014 x86_64 x86_64 x86_64 GNU/Linux
lsb_release -aDistributor ID: Ubuntu
Description: Ubuntu Trusty Tahr (development branch)
Release: 14.04
Codename: trusty
sorry for inconvenience caused.
my complex network configuration play a low-down trick.
What was your issue exactly? I’m having similar problems on current 14.04, on a laptop with standard wireless connection.
BTW, Adding /etc/init/lxc-unpriv-cgroup.conf from https://www.stgraber.org/2014/01/17/lxc-1-0-unprivileged-containers/ enabled me to setup a container, but broke my abbility to mount external hard drives with LXDE file manager or shutdown my computer with LXDE menus.
I have the same issue:
$ lxc-start -n onpoint -d
lxc_container: command get_cgroup failed to receive response
$ lxc-start -n onpoint
lxc_container: call to cgmanager_create_sync failed: invalid request
lxc_container: Failed to create cpuset:onpoint
lxc_container: Error creating cgroup cpuset:onpoint
lxc_container: failed creating cgroups
lxc_container: failed to spawn 'onpoint'
I running latest 14.04 with all updates installed, and I simply followed the steps at https://help.ubuntu.com/lts/serverguide/lxc.html
A lot of people seem to have this issue, and there are many bug reports open, e.g. https://bugs.launchpad.net/ubuntu/+source/lxc/+bug/1227092
Maybe the error message could be a bit more verbose?
Ok, the problem above was solved by simply rebooting the server. Apparently something related to the LXC stack or user permissions need to reload via reboot/re-login.
Hi
There’s something I don’t understand with this. You have to install an entire system just to have a application container ? That’s very heavy no ? Is there a way to create a container just for the app ?
Best Regards
Well, the main idea here is to use an OS/arch combo that’s known to be well supported and tested by proprietary software, so you indeed need a bit of duplication with the host system for that.
Now as for heavy, the actual duplicated content is about 350MB or 50MB compressed, so it’s not terribly light but it’s not gigantic either.
This worked great for me, I’ve been waiting a long time for something like this! The only trick to getting Hangouts to work was, I had to use an amd64 container image with an amd64 host. The i386 google talk plugin kept crashing.
Apparently the recent update fixed some of that, at least I used the 32bit Talk plugin for an hour this morning here and it worked fine.
If I’m understanding all of this correctly, LXC is like creating a virtual machine that shares much of the same installed code (kernel, libraries, maybe even icons and other data?), and it runs inside of a protected environment (the container). So in theory, I could set up a server running LXC and a few containers, and then log into a container on that server for different things.
Or I could run it locally and try out another distro, running it from a container. Or create a container specifically for “dangerous” software.
Sounds very advanced. I can’t wait to try it!
It’s a great example for how to run X Window applications in a container, however, you did not make it clear enough that it really does not much for added security.
The point that you make in passing (“can access the X server”) pretty much renders moot all security that might have been added in other places (the same applies with regards to recording audio via Pulse, which you also mentioned).
So, in my opinion, in should not even be suggested to do any of this to improve security — because it really does not, and it dangerous to feel safer when, in reality, you are not.
It doesn’t do much for privacy as eavesdropping is still possible, it does quite a bit for security though as software installed in that container won’t be able to trivially do things like replace your kernel, access your files, set scheduled tasks to re-execute themselves constantly, …
The use of the container ensures that when the container is off, nothing you installed in there can possibly still be running. The container doesn’t have access to your file system and is guaranteed to run as an unprivileged users (even those setuid binaries), therefore package installs and running untrusted setuid code won’t be able to do any more damage than a random unprivileged user could do on your machine.
I’m also a little leery of this as a security measure. I agree it’s better than running it outside of the container.
By giving it access to your uid alongside the X11/pulseaudio and other devices you’re giving the container a fair bit of attack surface.
Not only can it listen to every keypress or X11 event on the host system, it can also send keypresses and other events over the X11 socket. So it could, for example, create a script file on in the rootfs folder owned by the “real” host user, and send the keystrokes to run the script to a terminal window they have open.
Chromium is replacing the setuid sandbox, probably with LXC containers. See: https://code.google.com/p/chromium/issues/detail?id=312380
This should be behind a flag soon, and I expect that it’ll compose fine with your use of containers, so you won’t need to disable a layer of sandboxing anymore.
Awesome, looking forward to it!
User namespaces definitely are a great fit for that kind of sandboxing and allowing users to avoid using the setuid wrapper while still benefiting from the sandbox will be a great improvement!
I use xpra (packaged in Debian) to run GUI apps in kvm. xpra comes with a client and server. Inside the virtual machine it starts pulseaudio and a dummy X server and forwards video+audio to the xpra process on the host which displays each application window like it would run directly on the host.
I use xpra daily at work to run eclipse, chrome, flash, …
I’d love to hear from your experiences running xpra with containers! I’m just starting to learn about containers.
Hi!
I just tried x2go with LXC and it works well as for me.
I use x2go as well and it works great. If you are on Ubuntu you can also use the x2go browser plugin setup. With that from the Host you can get your desktop from the Container by just pointing to its IP. (x2go.org)
I’ve also used the HTML5 remote desktop tool called Guacamole (guac-dev.org). It takes a bit more setup than x2go but it works really well also and only requires a browser.
Hi!
I just recently tried x2go with LXC and it works well as for me.
This seems to be needed before installing Chrome:
lxc-attach -n precise-gui -- apt-get install libnspr4 libnss3 libxss1 libcurl3 xdg-utils libv4l-0 librtmp0 libv4lconvert0 -y
Does anyone have an example of how to do this via a Dockerfile? Thanks.
Regarding Steam & NVIDIA: I’m able to run Steam in an unprivileged container, but when it starts I get this error:
Sorry, I messed up with the format. Here’s the comment:
Regarding Steam & NVIDIA: I’m able to run Steam in an unprivileged container, but when it starts I get this error:
OpenGL GLX context is not using direct rendering, which may cause performance problems.For more information visit https://support.steampowered.com/kb_article.php?ref=9938-EYZB-7457.
The client works OK, but I can’t play games.
This are the mount entries of my config file:
lxc.mount.entry = /dev/dri dev/dri none bind,optional,create=dirlxc.mount.entry = /dev/snd dev/snd none bind,optional,create=dir
lxc.mount.entry = /tmp/.X11-unix tmp/.X11-unix none bind,optional,create=dir
lxc.mount.entry = /dev/video0 dev/video0 none bind,optional,create=file
lxc.mount.entry = /dev/nvidia0 dev/nvidia0 none bind,optional,create=file
lxc.mount.entry = /dev/nvidiactl dev/nvidiactl none bind,optional,create=file
I’ve also set this additional environment variable in the “start-steam.sh” script:
LD_PRELOAD=/usr/lib/i386-linux-gnu/mesa/libGL.so.1My host system is running trusty with nvidia-331 packet installed. In the container (running precise) I also installed the nvidia-331 packet, but got a few warnings, being the most relevant to me:
First Installation: checking all kernels...dpkg: warning: version '*-*' has bad syntax: version number does not start with digit
It is likely that 3.13.0-24-generic belongs to a chroot's host
What I’m doing wrong?
I was having the same problem. I solved it by installing the same nvidia driver in the container that I have on my host machine. While I was at it, I installed mesa-utils:i386 so I could check my progress by running glxinfo | grep “direct rendering”.
I didn’t use LD_PRELOAD, but I did add this to my container config to make sure /dev/nvidia* could be used:
lxc.cgroup.devices.allow = c 195:* rwm
I also made sure uid 1000 (the account I use to log in to my container) doesn’t get remapped, so it has the same device permissions that my host account has:
lxc.id_map = u 0 100000 1000
lxc.id_map = g 0 100000 1000
lxc.id_map = u 1000 1000 1
lxc.id_map = g 1000 1000 1
lxc.id_map = u 1001 101001 64535
lxc.id_map = g 1001 101001 64535
(And I applied the chown -R command in Stéphane’s post.)
P.S.
One of the dependencies installed by my nvidia driver failed to install because of a conflict with the /tmp/.X11-unix directory mounted by my container. I ran sudo umount on that directory, then apt-get install -f to complete the installation, and then restarted the container to get the mount back.
I guess it is wishful thinking if one could also put drivers in the LXC right?
Say, opensource in the ‘my box, get lost NSA croonies’ and binary blob from 3d card maker, running inside a container? hehe would be awesome but obviously too low level. But, possible in the future somehow?
For the .desktop file, I put it in ~/Desktop and dragged it on the launcher (far left of the Ubuntu Unity Desktop):
#!/usr/bin/env xdg-open
[Desktop Entry]
Version=1.0
Type=Application
Terminal=false
#Icon[en_US]=gnome-panel-launcher
Icon[en_US]=/home/ivan/.local/share/lxc/chrome/rootfs/opt/google/chrome/product_logo_256.png
Icon=/home/ivan/.local/share/lxc/chrome/rootfs/opt/google/chrome/product_logo_256.png
Name[en_US]=Chrome
Exec=/home/ivan/.local/share/lxc/chrome/start-chrome %U
Comment[en_US]=Access the Internet
Name=Chrome
Comment=Access the Internet
Hi. After a kernel update? Now when running unpriv. containers, the /proc and /sys is owned by nobody:nogroup (as in the mailing lists/discussion regarding shmem). Anyway, this now prevents the various things like skype, chromium etc to chroot into /proc or so…
So what will happen, or how to go about fixing this?
Any tips?
Following your instructions on Ubuntu 14.10 I get the following error
running sudo lxc-start -n utopic-gui -F
newuidmap: uid range [0-1000) -> [100000-101000) not allowed
lxc-start: Error setting up child mappings
lxc-start: Error requesting cgroup chown in new namespace
newuidmap: uid range [0-1000) -> [100000-101000) not allowed
lxc-start: failed to set up id mapping
lxc-start: failed to spawn ‘utopic-gui’
lxc-start: The container failed to start.
lxc-start: Additional information can be obtained by setting the –logfile and –logpriority options.
Any idea what goes wrong?
I love the idea of running chrome in more secured environment.
Thanks
Marc
Can you do a tutorial on accessing the gui of a system container at the host’s tty (with CTRL+ALT+Fn)? There is alot of confusing info out there on how to properly set up the host and containers tty so you can get a login screen for the container. thanks a bunch for this and for lxc!
7 years later and I still cannot find a definitive yes or no to this question…
Google Chrome 42 can run in an unprivileged lxc container without having to use the “–disable-setuid-sandbox” flag.
For me, chrome seems to work fine even without –disable-setuid-sandbox.
Can anyone else comment their mileage with it? Chrome version is 42.
chrome worked as the posters above claim for me, until I upgraded the host system to Vivid. Now my trusty chroot can’t run chromium, no matter how much I try to enable/disable the sandbox. ☹
I had to disable xauth (on 15.04 host) to get it working.
Ok, I finally got it to work with the below extra setup file:
To get my lxc contained apps to use HWA, I had to replace /dev/dri with /dev/ati in the config and install the same fglrx drives as my host (I downloaded the source deb’s from launchpad and they compiled fine)
Your script does not work for me.
Can you confirm that? thanks.
-rsd
You can juste use that in your setup script.
XAUTH_FILE=”${LXC_ROOTFS_PATH}/home/ubuntu/.Xauthority”
rm $XAUTH_FILE
touch $XAUTH_FILE
xauth extract – $DISPLAY | xauth -f $XAUTH_FILE merge –
Thanks Stéphane for all your great info.
You’ve saved me countless hours slicing up physical servers into LXC containers for my high speed hosting company.
Keep up your Great Work!
Anyone using on 15.04?
It seems to need a few tweaks to get X DISPLAY working.
Any news on 15.04 ?
In my setup, my host is 15.04, and the lxc is 14.04, following the above recipes, I can’t get it working … nor even via ssh X11 setup … arhg … :/
Thanks
I just had some trouble getting Debian 8 “Jessie” up and running with a bindmount setup of the X11-socket. The problem turned out to be systemd-tmpfiles which cleared out tmp on boot, including my X11-socket.
To disable this behaviour I copied /usr/lib/tmpfiles.d/tmp.conf to /etc/tmpfiles.d/ and commented out the line “D /tmp 1777 root root -“.
how would i do this using lxd? not sure how to access or alter the config file.
newcomer to this business…trying to learn through other’s examples
thanks
bill
I’m looking at running a full desktop environment in the container. Is this possible?
Also how do you install virtualbox inside a container so, I can run other os’s (windows etc)?
Thnks
I have got the following assignment.I am new to Linux container.Presently i am learning Linux container.And have to implement a featuree.Someone please suggest me what features that can be implemented..Assignmenet submission date is 28/10/2015
the following is my case study.
(Container-Complex)
Choose a container library, say LCX or libcontainer.
Add a significant feature that is not built in.
Example feature could be security , a Windows-like event propagation model, an indexing system for supporting databases.
Adding the feature would require:
a specification of the feature;
a design of how the feature would be integrated into a container;
choosing an appropriate external module / library that implements parts of the feature
patching / integrating it into the Container library with appropriate additional code
Thanks in advance,
Rashmi
I also experienced problems with xauth in Ubuntu 15.04. My solution was to add permissions for local connections to xhost. Please note that this was developed for running one container at a time and may grant other containers or users on the same machine access to your X server.
xhost +local:
Hi, Stephane, your blog pages here are super! I am beginning to test out the container technology (docker, lxc) and your pages here have been very instructive. The posts 9 (GUI) and 7 (unprivileged container) have been of immediate interest to me, and I was able to use them in my work. Excellent. Now, I have some questions.
My questions are related to “LXC” and “LXD” (https://linuxcontainers.org).
I understand that in the “old way” (LXC), commands such as “lxc-create”, “lxc-start” can be used to work with containers (as described in these blog pages).
In the “new way” (LXD), the command “lxc” can be used to work with containers.
I noticed that in the old way containers are located under the folder /var/lib/lxc (or ~/.local/share/lxc), whereas in the new way containers are located under the folder /var/lib/lxd. And, I have yet to find the documentation as to how to run an unprivileged container or how to run GUI programs in the new way. So, here are my questions.
1. Is it possible to run an unprivileged container or a GUI program from a container using hte new way? If so, any documentations (similar to these blog pages)?
2. If containers are created and worked on using the old way, will I be able to import them easily to the LXD way of doing thing later on?
I tried with ‘lxc config add share_name disk source=.. path=..’
Looks it work fine! verified with a container runs Ubuntu 16.04 on 14.04 host.
BTW, you need to add /home/dpu/.Xauthority to container as ‘disk’ as well.
I just get rid of all the idmap things by deleting the default ‘ubuntu’ user in container
then add same username as host(which is also the first which has id:1000).
In this way, both user has exactly uid/gid.
devices:
dev_snd:
path: /dev/snd
source: /dev/snd
type: disk
dev_x11:
path: /tmp/.X11-unix
source: /tmp/.X11-unix
type: disk
share_dri:
path: /dev/dri
source: /dev/dri
type: disk
share_xauthority:
path: /home/username/.Xauthority
source: /home/username/.Xauthority
type: disk
Hello together,
if followed the instructions above exactly. But at the point to first start the container i got the following Error-Message:
lxc_container: cgmanager.c: lxc_cgmanager_create: 299 call to cgmanager_create_sync failed: invalid request
lxc_container: cgmanager.c: lxc_cgmanager_create: 301 Failed to create bfqio:precise-gui
lxc_container: cgmanager.c: cgm_create: 646 Error creating cgroup bfqio:precise-gui
lxc_container: start.c: lxc_spawn: 861 failed creating cgroups
lxc_container: start.c: __lxc_start: 1080 failed to spawn 'precise-gui'
lxc_container: lxc_start.c: main: 342 The container failed to start.
lxc_container: lxc_start.c: main: 346 Additional information can be obtained by setting the --logfile and --logpriority options.
My system:
$ uname -a:
Linux TQ 3.13.0-68-lowlatency #111+7.0trisquel2 SMP PREEMPT Tue Nov 10 04:15:48 UTC 2015 x86_64 x86_64 x86_64 GNU/Linux
$ lsb-release -a:
No LSB modules are available.
Distributor ID: Trisquel
Description: Trisquel GNU/Linux 7.0, Belenos
Release: 7.0
Codename: belenos
Does anyone had this issue and can help me?
Thanks a lot!!!
Hi, this tutorial used to work perfectly until recently. The exact same one tried on a fresh install of Trusty (host) with Precise (guest) does not work anymore due to display problems. The quite insecure solution ‘xhost +’ partially solve the access to the X server problem but it seems there have been modifications somewhere which prevent things to work smoothly. Any update planned for this tutorial? Thanks a lot!
In Steam I only get a messenger and nothing else. It seemed to install fine. Did I miss something?
When running a headless Ubuntu 14.x (or 16.x) server, how do you get a desktop environment to work within an unprivileged container?
If container is not starting with output
lxc_start.c: main: 344 the container failed to start.
then read this fix – http://unix.stackexchange.com/questions/176973/userns-container-fails-to-start-how-to-track-down-the-reason
(I just installed cgroup-bin and libpam-systemd)
I am trying to run an unprivileged container with USB pass through.
My host is Ubuntu 15.10, my container is CentOS 6
I have followed all of your actions above, with the following exceptions:
I did not implement a setup script. For now I just want the device
My host USB device is
brw-rw-rw- 1 root disk 8, 17 Jun 1 11:50 /dev/sdb1
lxc.cgroup.devices.allow = b 8:* rwm
lxc.mount.entry = /dev/sdb1 /dev/sdb1 none bind,optional,create=dir
I do not get any errors in starting, but my container does not have any device called
/dev/sdb1
It would be helpful if you could give some suggestions
Error in 16.04, I’m trying to get this running on 16.04 and the container is also xenial, but I keep getting the same error.
[1214:1214:0603/060004:ERROR:browser_main_loop.cc(271)] Gtk: cannot open display: :0.0
Hey Stéphane,
Is there any way in LXD to do what you do here with the UID/GID mapping, except for one user? It looks like LXD doesn’t have the same flexibility, but I am maybe missing something.
Cheers.
May I request you to make a post on doing the above for a container created using LXD?
Very much hoping for an update of this article for LXD 😉
Note also this question http://askubuntu.com/q/820798/598136
Be careful if you try to upgrade the distribution – for whatever reason, the xenial amd64 image doesn’t come with network preconfigured:
$ lxc-create -t download -n xenial-test — -d ubuntu -r xenial -a amd64
Using image from local cache
Unpacking the rootfs
—
You just created an Ubuntu container (release=xenial, arch=amd64, variant=default)
To enable sshd, run: apt-get install openssh-server
For security reason, container images ship without user accounts
and without a root password.
Use lxc-attach or chroot directly into the rootfs to set a root password
or create user accounts.
$ lxc-create -t download -n xenial-test — -d ubuntu -r xenial -a amd64^C
$ lxc-start -n xenial-test
$ lxc-attach -n xenial-test — ifconfig eth0
eth0 Link encap:Ethernet HWaddr xx:xx:xx:xx:xx:xx
inet6 addr: xxxx::xxx:xxxx:xxxx:xxxx/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:14 errors:0 dropped:0 overruns:0 frame:0
TX packets:6 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:1782 (1.7 KB) TX bytes:508 (508.0 B)
$ lxc-attach -n xenial-test — ping google.com
ping: unknown host google.com
Network does work out of the box in the trusty amd64 image, though.
i can’t find the file config of container precise-gui. anyone can help me?
Hi!
What about installing kodi on a raspberry pi with lxc?
Thanks in advance.
Isn’t it more secure to run apps through SSH using X11 forwarding? I guess this would prevent the security issues mentioned: “pulseaudio: possibly recording you”, “X11: possibly doing key logging or taking pictures of your screen”, dri/snd devices possibly doing the same and it would not be a problem to run the container while doing sensitive work.
I was able to run GUI apps in LXC with SSH using X11 forwarding but with the method mentioned in this post, I get the following error when running “lxc-start lxc -F”, any idea?
lxc-start: lxc: conf.c: lxc_map_ids: 2999 newuidmap failed to write mapping “newuidmap: uid range [1000-1001) -> [1000-1001) not allowed”: newuidmap 14486 0 100000 1000 1000 1000 1 1001 101001 64535
lxc-start: lxc: start.c: lxc_spawn: 1708 Failed to set up id mapping.
lxc-start: lxc: start.c: __lxc_start: 1939 Failed to spawn container “lxc”
lxc-start: lxc: tools/lxc_start.c: main: 330 The container failed to start
lxc-start: lxc: tools/lxc_start.c: main: 336 Additional information can be obtained by setting the –logfile and –logpriority options
“Running applications like Chrome in containers is a smart move for better security and isolation, especially when dealing with untrusted binaries. I remember struggling with container configurations, particularly with mounting PulseAudio and ensuring proper X11 access. If you’re setting up environments for specific tasks, such as learning to
install Python on Ubuntu 24.04, containerization can help maintain a clean and controlled system. Thanks for sharing this guide—it brings back some valuable lessons!”